Who’s tracking your phone?
By now you will have heard how the FBI is using cellphone data to track down people who were at the January 6 storming of the Capitol. Early last year, you may have seen the orange-dots-on-black maps that tracked a group celebrating spring break in Fort Lauderdale as they headed home — potentially carrying COVID. What about you? Have you been in any situations lately where you think someone might have been tracking your phone?
Whether you like or don’t like the idea of being tracked by your cellphone, it is happening!
Not because you are a suspect in a crime. Not because you could be carrying a virus. No, you are being tracked because you are a valuable marketing asset! In fact, years of your location data has probably already been recorded, sold and re-sold multiple times, without you getting a single penny for it!
By now you may also be wondering, “Virginia, what does phone location data have to do with emergency preparedness?” As you’ll see, there are a couple of interesting angles to this story.
Assumptions behind this Advisory
First, we assume you have a smartphone. If you’re like most people, you count on your phone as your main communications tool for emergencies. How your phone is set up could play an important role in its usefulness.
Second, we think everyone interested in preparedness should be knowledgeable about security. We assume this includes phone security.
Before we go any further, here’s a disclaimer. Cellphone technology changes monthly, maybe weekly! Please confirm what you read here today with experts (your phone manufacturer, the app developer, your IT consultant, etc.) before you take any actions!
The vocabulary of phone tracking
And before we jump into what I’ve learned this week, I have to start with some vocabulary. (I had to look up these words myself.)
- A GPS chip in the phone is what allows it to be tracked. The chip reveals location data: where your phone was and how long it stayed there. (GPS refers to the Global Positioning System, operated and maintained by the U.S. Air Force for “Space-Based Positioning, Navigation, and Timing.”) Satellites, cell towers and Wi-Fi can all be used to pinpoint the location of your phone.
- Metadata is the basic info about a phone message. It consists of who you are (your device, not your name), who you’re talking to (device), and when you’re talking.
- Content is what you are actually saying or sending by message. Your content can be encrypted for privacy.
- Encryption is a process whereby a message is converted into code, making it impossible to read unless you have the key to the code.
Of course, we rely on all this information on ordinary days and during emergencies.
GPS capability helps us chat with friends, make business arrangements and find our way there. It lets us check on what the weather’s going to be like, and figure out where to get gas.
In an emergency our phone uses the same technology. We can check to be sure family is OK, locate the fire or traffic jam, find our way to a shelter. If we’re trapped under a fallen wall, our phone could help direct First Responders to our rescue.
Some of these functions are built into the phone. We can add many other functions using apps – map apps, news apps, social apps, earthquake alerts, gaming, chat, roadside assistance, etc. etc. You will be interested to know that the average person has 40 apps installed on their phone — of the over 2 million available! That average person only uses about 20 of them, however. (As you might imagine, younger adults use more than older adults.) You can get more interesting details of phone app usage here.
So, phones and apps represent a lot of convenience.
The real value though, and the reason people are tracking your phone, is the information that apps capture about your location.
When you use your phone and apps, you are agreeing to be tracked in real time. Companies tell you they are tracking your phone in order to “Give you a better user experience” or “Improve service.” At the same time, many of the apps, and particularly the free ones, collect far more than the essential info they need.
They combine your location data with other users’ data and sell it to organizations that build and then in turn sell detailed user profiles for marketing purposes. Hundreds of companies buy the compiled user profile data. Examples are banks, insurance companies, credit companies, airlines, and retail giants like Nike and Amazon. Oh, and political parties!
Can the government buy this data, too? Typically, law enforcement has to prove why they need the data. But there’s been recent reporting of Customs and Border Protection (CBP) and Immigration and Customs Enforcement (ICE) spending thousands of dollars on location data – without being authorized to do so. The ACLU is suing for infringement of privacy.
However the lawsuits work out, you can pretty much assume that some of your personal location information has been collected and passed along to private and perhaps even governmental agencies. And this won’t stop.
What can you do to keep the world from tracking your phone?
Here are simple things we all can do that will make it harder for our location to be traced.
- Turn off the radios (think Spotify) on your phone, whether they are cellular or wi-fi.
- Even if your phone is off, though, its location can be found because Wi-Fi and Bluetooth still receive data. The easiest way to stop this is to turn on the “Airplane Mode” feature.
- Go to “Settings,” “Privacy” and “Location settings” on your phone, and adjust. Apple also has a setting to “limit ad tracking.” (A lot of the apps you like probably need location settings, so be careful in shutting things off entirely.)
- Shut the phone down completely and take out the battery. Of course, then you can’t use the phone at all!
If you read any crime novels like I do, at this point you will be asking, “What about using a burner phone? (For the non-crime reader, these are pre-paid cellphones used just a couple of times and then trashed.) If you want to use a burner to avoid being identified, be sure to buy with cash (away from where you usually shop), keep your calls short, and remove the SIM card before you toss the phone. These phones can still be located but even if the phone is located there’s theoretically no link to you as an individual.
What about protecting the messages you do send?
Location is metadata, and can be tracked in a number of ways and by a whole raft of commercial enterprises. What’s in your messages is “content.” Content is a lot harder for people to get to – and pretty easy for you to make more secure.
For security, insist on encrypted messages. I didn’t really realize it, but many of our most popular messaging services automatically encrypt what you send – as long as the person on the other end of the message has the same service (and thus the key to the encryption).
For several years my family and I have been using WhatsApp to send messages and photos. In 2016 WhatsApp announced end-to-end encryption. (WhatsApp had been purchased by Facebook a couple of years earlier.) In 2018, Apple’s iMessage and FaceTime also announced end-to-end encryption.
Sounds good, eh? But it’s important to remember that if these companies store or back up your messages, the messages may be available at a later time. And since these are for-profit companies, we cannot know exactly how they intend to approach privacy in the future.
My research for this Advisory suggests that if you are concerned about having a good, free and private encryption message service, you should look into the Signal Messaging app. It’s a non-profit company that has always been dedicated to end-to-end encrypted calling and texting.
Caution: In recent months the demand for “privacy” online has led to dramatic growth for Signal, and experts are watching to see how the company will respond to this surge in new users.
So you’ve set up your phone for a better level of privacy. Now what?
What else can you do to your phone to yourself from being tracked, surveilled or hacked? Here’s a last list of suggestions. I hope most of these recommendations are familiar to you!
- Set up a password on your phone, the longest one possible. Don’t be like the 70% of people who use the same password for multiple accounts!
- Consider using a fingerprint or faceID instead of a passcode. Harder for a thief to get into your phone. On the other hand, easier for police to force you to open it.
- Don’t charge your phone in public places like airports or shopping centers. You don’t know if that outlet itself has been compromised and thus might be transmitting your private data while all you think is that you’re charging the phone.
- Use the same caution when picking public “hotspots” – like a Starbucks – for connecting to the internet.
- Remember that companies can be subpoenaed to give up your data. You may not even know it has happened.
Finally, keep track of your cellphone! Over 70 million are lost or stolen each year!
Go onto YouTube and you can see video after video of people’s phones being stolen right out of their hands as they are standing talking on the street. Most of these “grab and run” thieves zip by on a bike or scooter and before you realize it, your phone hand is empty! We wrote about “scooter” thefts last year, when there was a rash of them in San Francisco.
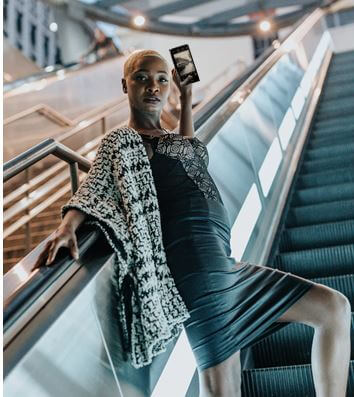
And if you’re still remembering the image at the top of this page, it is meant to represent another situation where phones get stolen. You are going up the escalator, the thief is going down, and BINGO, your phone has disappeared.
I found a couple of inexpensive items that might be useful for forgetful or careless types.
First is a lanyard to keep you from walking away from your phone. This one comes in different colors, even in two-packs so you can change colors to fit your outfit (or share with another family member).

Or maybe you’d prefer a wrist strap to you can keep the phone handy even when your hands are otherwise full. And a wrist strap would keep that escalator thief from grabbing and getting away!

If you’re worried about your phone slipping out of your pocket, or being slipped out by a pick-pocket, consider this. It uses a magnet to “pin” your phone securely in place inside your pocket or purse.

One last note about cellphone security.
Your security depends on the person you are sending to having good security, too. I love this oh-so-timely quote: “Think of it as herd immunity. The more people practice good security, the safer everyone else is.”
Virginia
Your Emergency Plan Guide team
P.S. What other suggestions do you have? Let us know. Dealing with our phones is not going to get any easier.


 We regularly look at what I’ll call “common security devices” – outdoor lights, motion-activated lights, including the very popular Ring doorbell camera.
We regularly look at what I’ll call “common security devices” – outdoor lights, motion-activated lights, including the very popular Ring doorbell camera.

